Shielding Vital Data from Evolving Digital Attacks in UAE
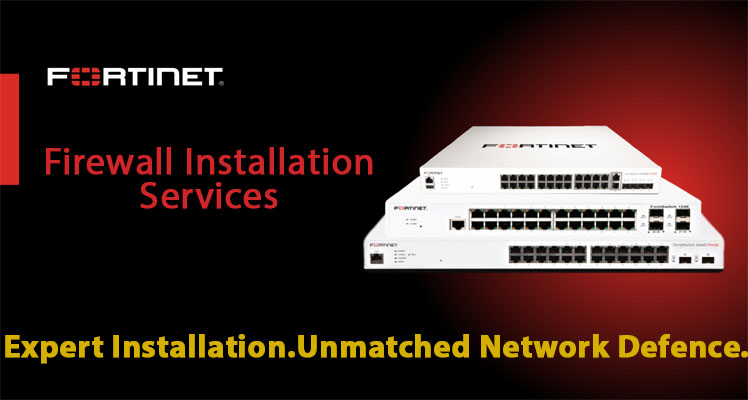
UAE's data centers constitute the core of this ecosystem. To ensure their security, they require an integrated approach that combines Cybersecurity for Data Centers, Data Center Firewalls, Data Center Encryption, Data Center Threat Detection, Rack-level Security, and Server Room Security. Together, these components create the base of a secure, resilient and future-proof IT infrastructure.
click on the below link for more information:
https://tektronixllc.ae/data-center-perimeter-security-solutions/
UAE's data centers constitute the core of this ecosystem. To ensure their security, they require an integrated approach that combines Cybersecurity for Data Centers, Data Center Firewalls, Data Center Encryption, Data Center Threat Detection, Rack-level Security, and Server Room Security. Together, these components create the base of a secure, resilient and future-proof IT infrastructure.
click on the below link for more information:
https://tektronixllc.ae/data-center-perimeter-security-solutions/
Shielding Vital Data from Evolving Digital Attacks in UAE
UAE's data centers constitute the core of this ecosystem. To ensure their security, they require an integrated approach that combines Cybersecurity for Data Centers, Data Center Firewalls, Data Center Encryption, Data Center Threat Detection, Rack-level Security, and Server Room Security. Together, these components create the base of a secure, resilient and future-proof IT infrastructure.
click on the below link for more information:
https://tektronixllc.ae/data-center-perimeter-security-solutions/
0 التعليقات
0 المشاركات
17 مشاهدة
0 معاينة